Presenter

Ghada Almashaqbeh, UConn
Ghada is an assistant professor in the Computer Science and Engineering department at UConn. She is also an affiliated member at the Connecticut Advanced Computing Center (CACC) and the Engineering for Human Rights Initiative. Before joining UConn, she spent a while exploring the entrepreneurship world. She cofounded CacheCash, a startup that came out of her PhD thesis! and she was a Cryptographer at NuCypher. Now, she is a scientific advisor at Sunscreen Tech and The Melon, and a 2023 fellow at the Foresight Institute. Her research interests cover cryptography, computer systems security, and privacy, with a focus on blockchain-based systems and distributed cryptographic protocols. Her research is supported by NSF, Protocol Labs, and UConn Research Excellence Award.
Summary:
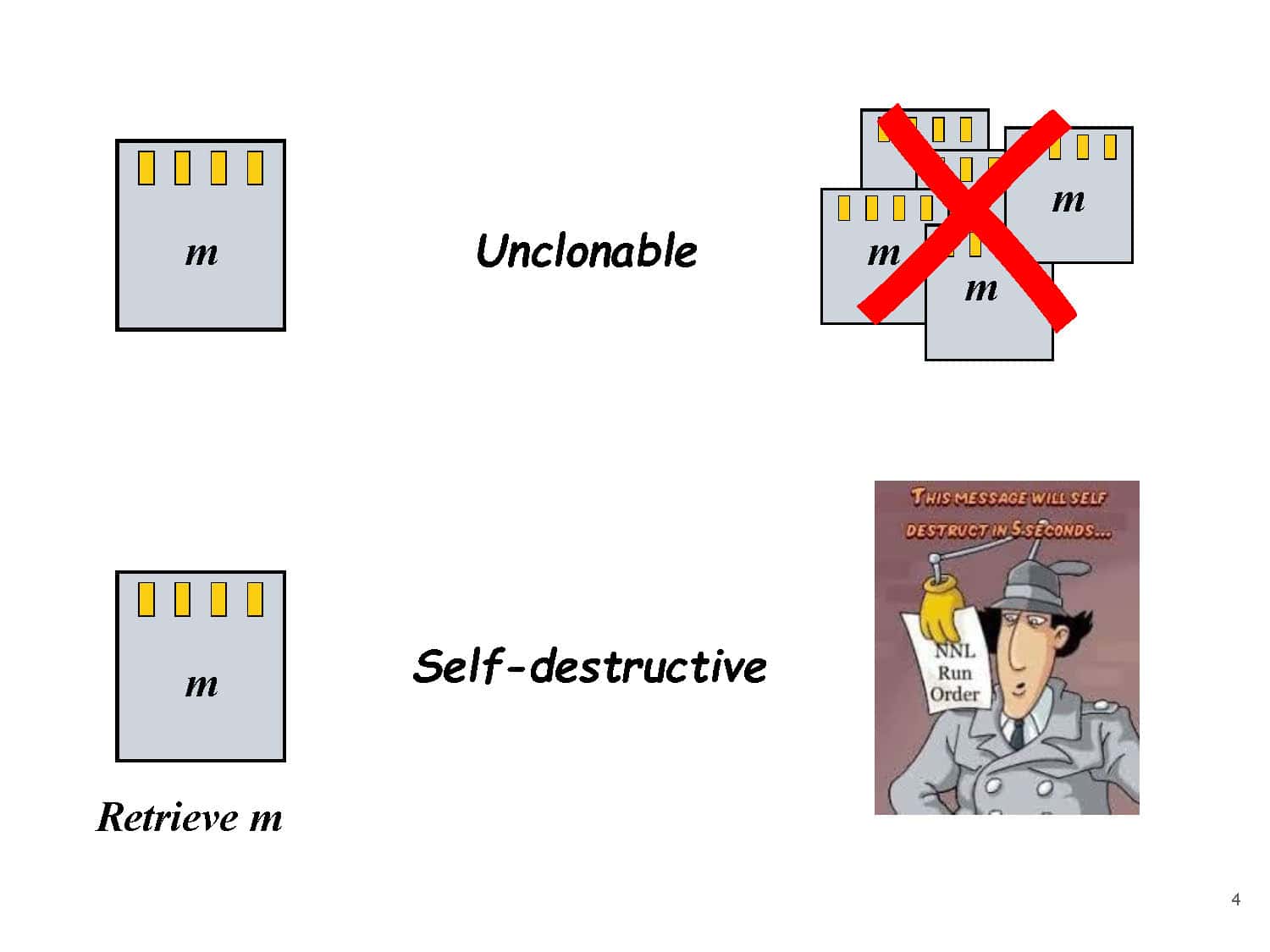
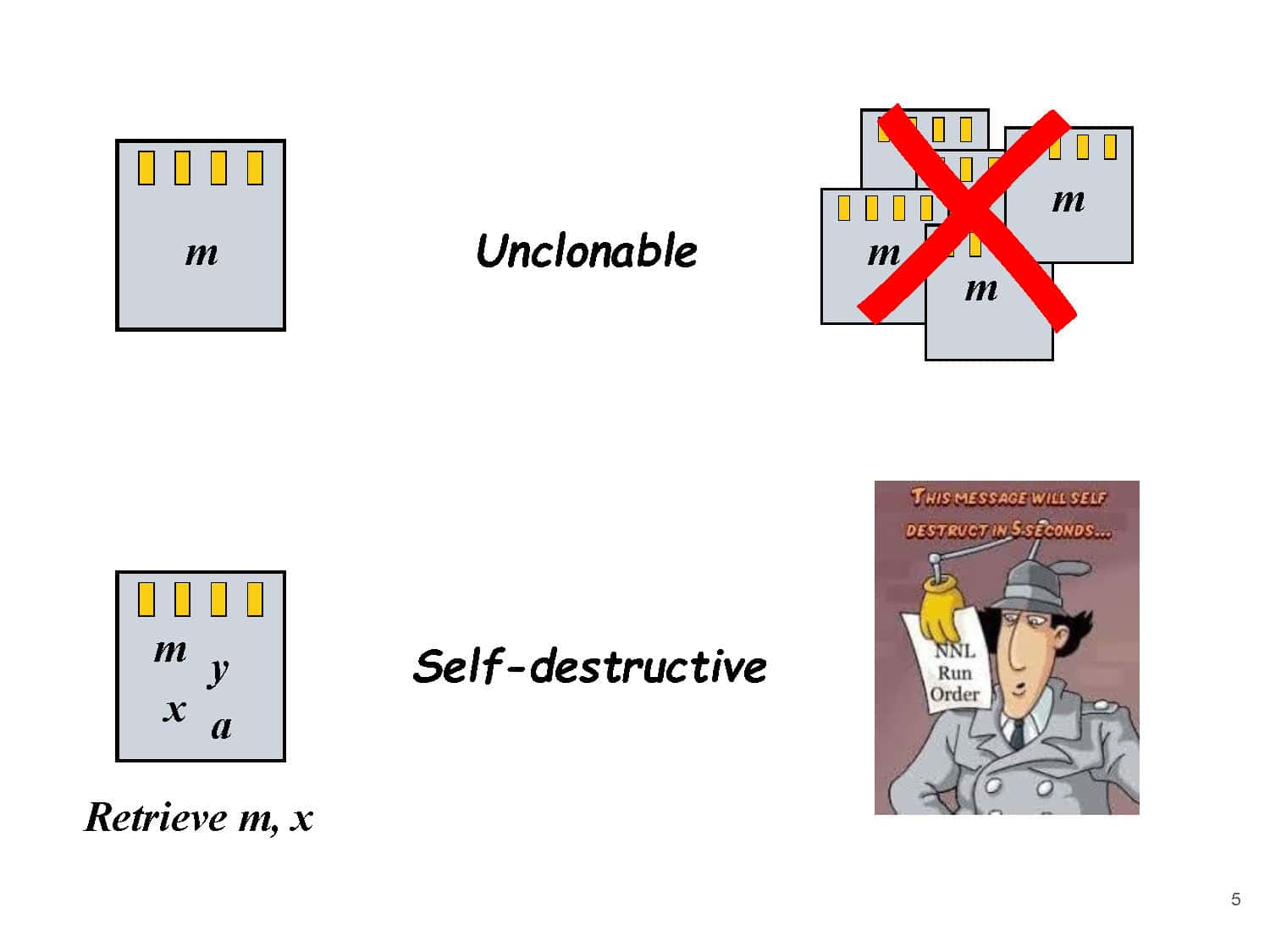
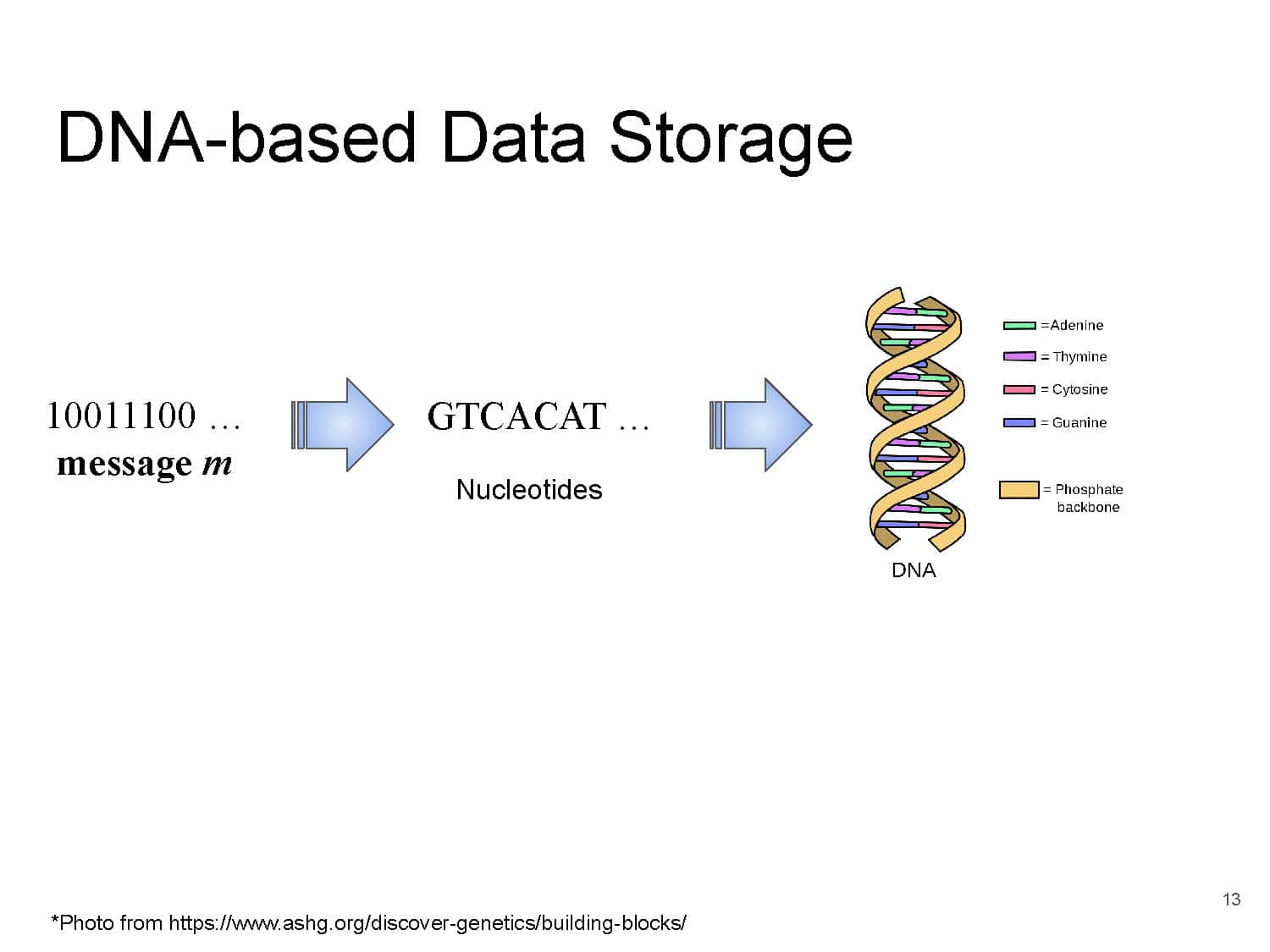
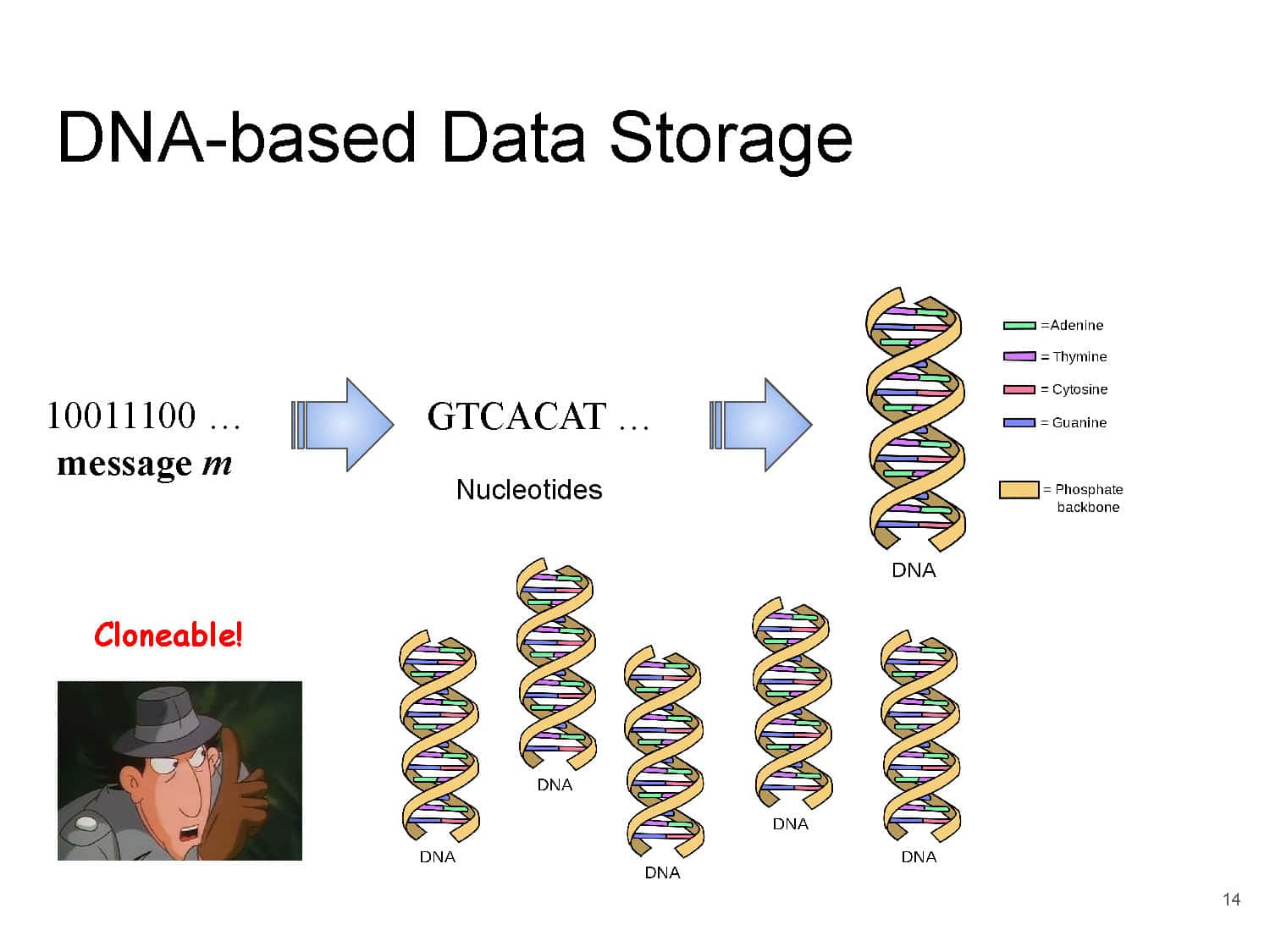
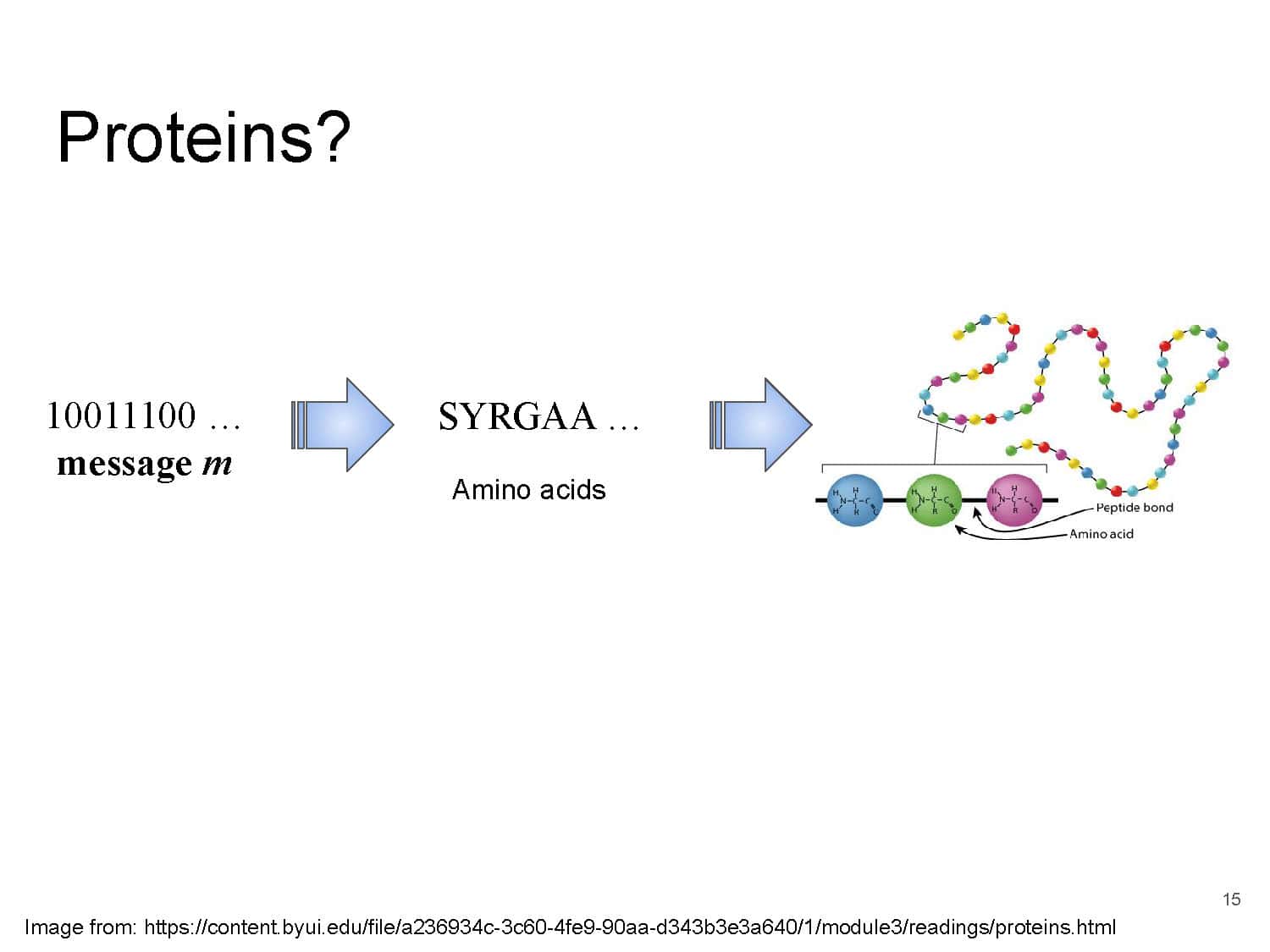
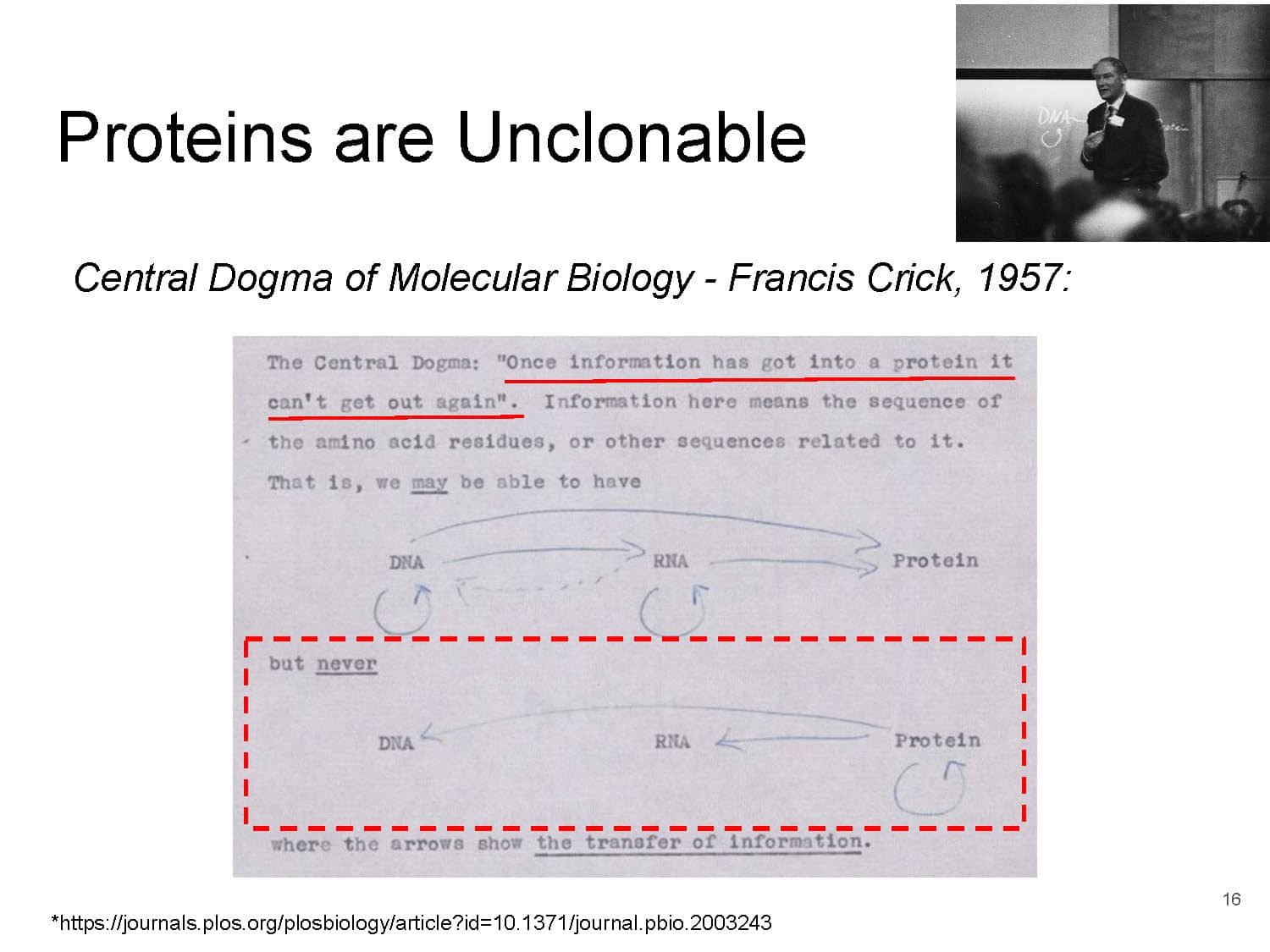
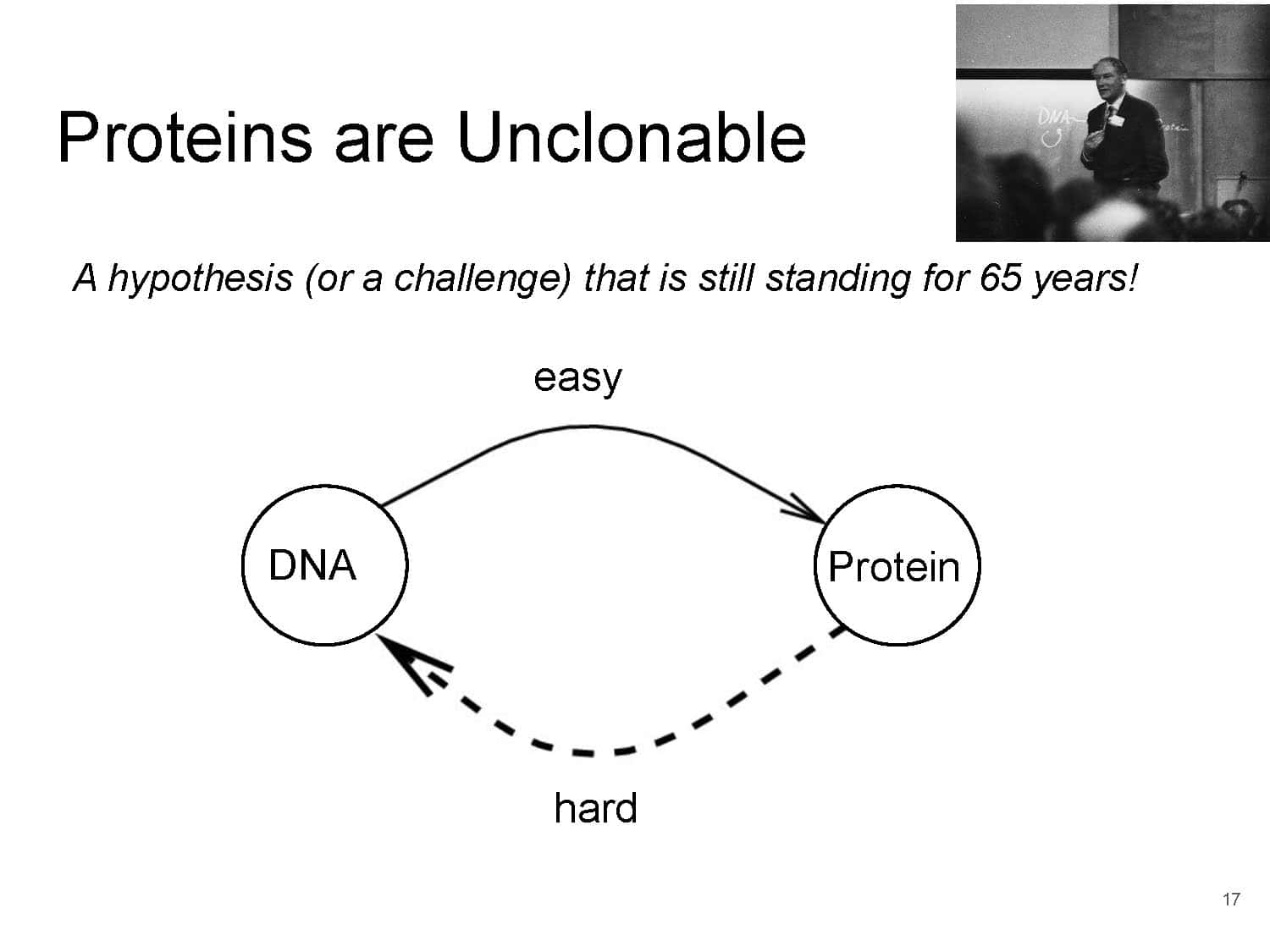
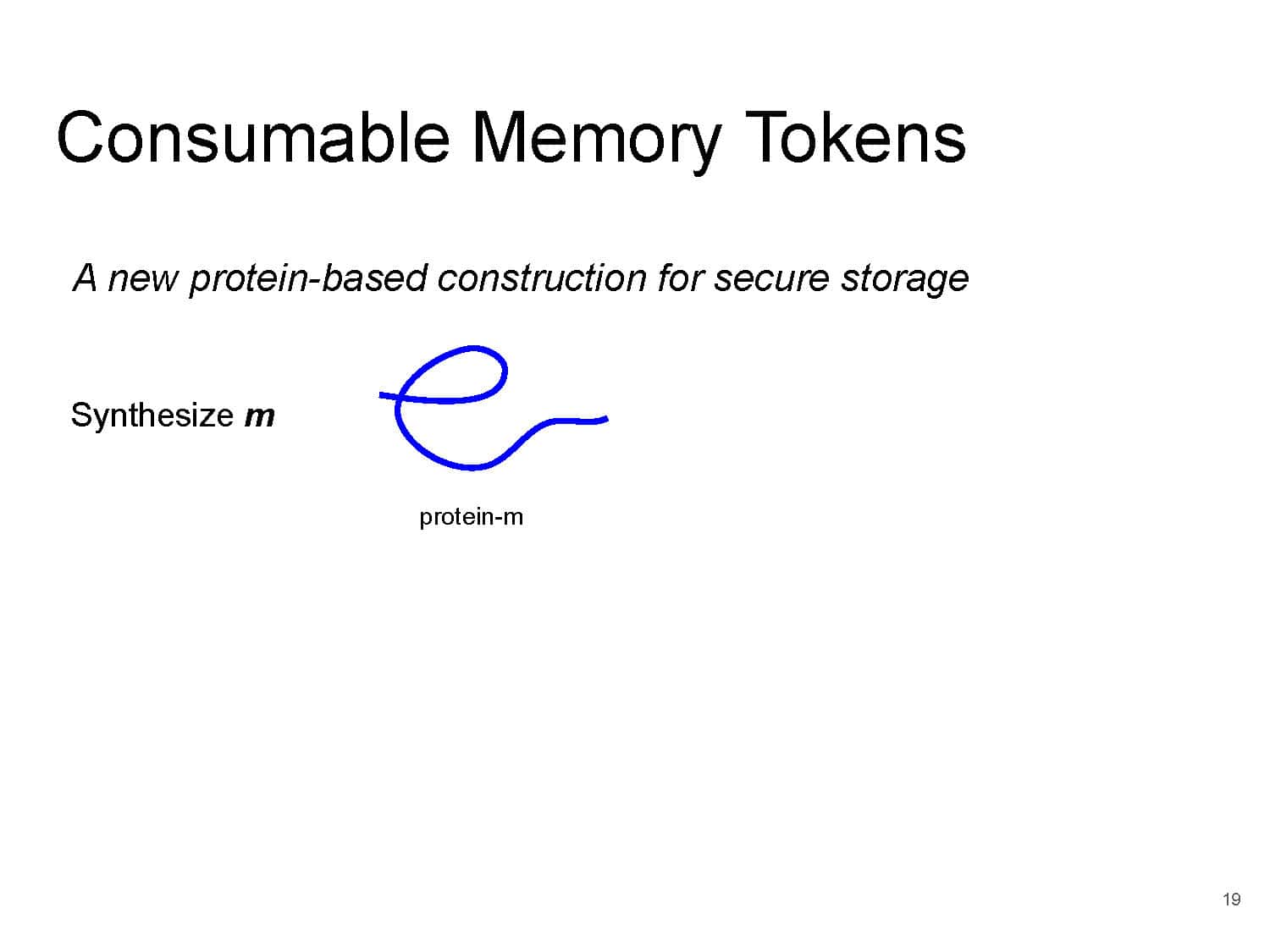
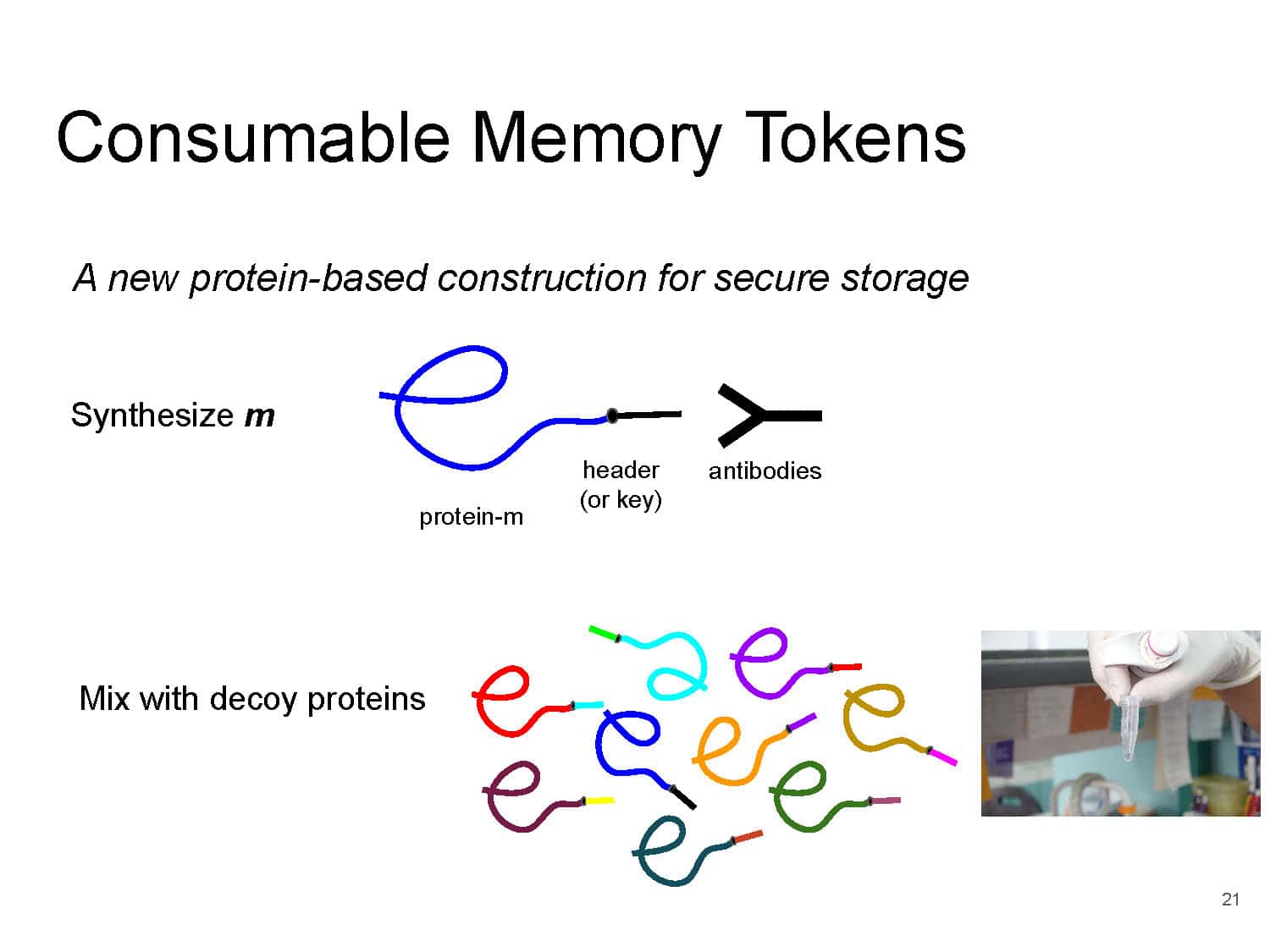
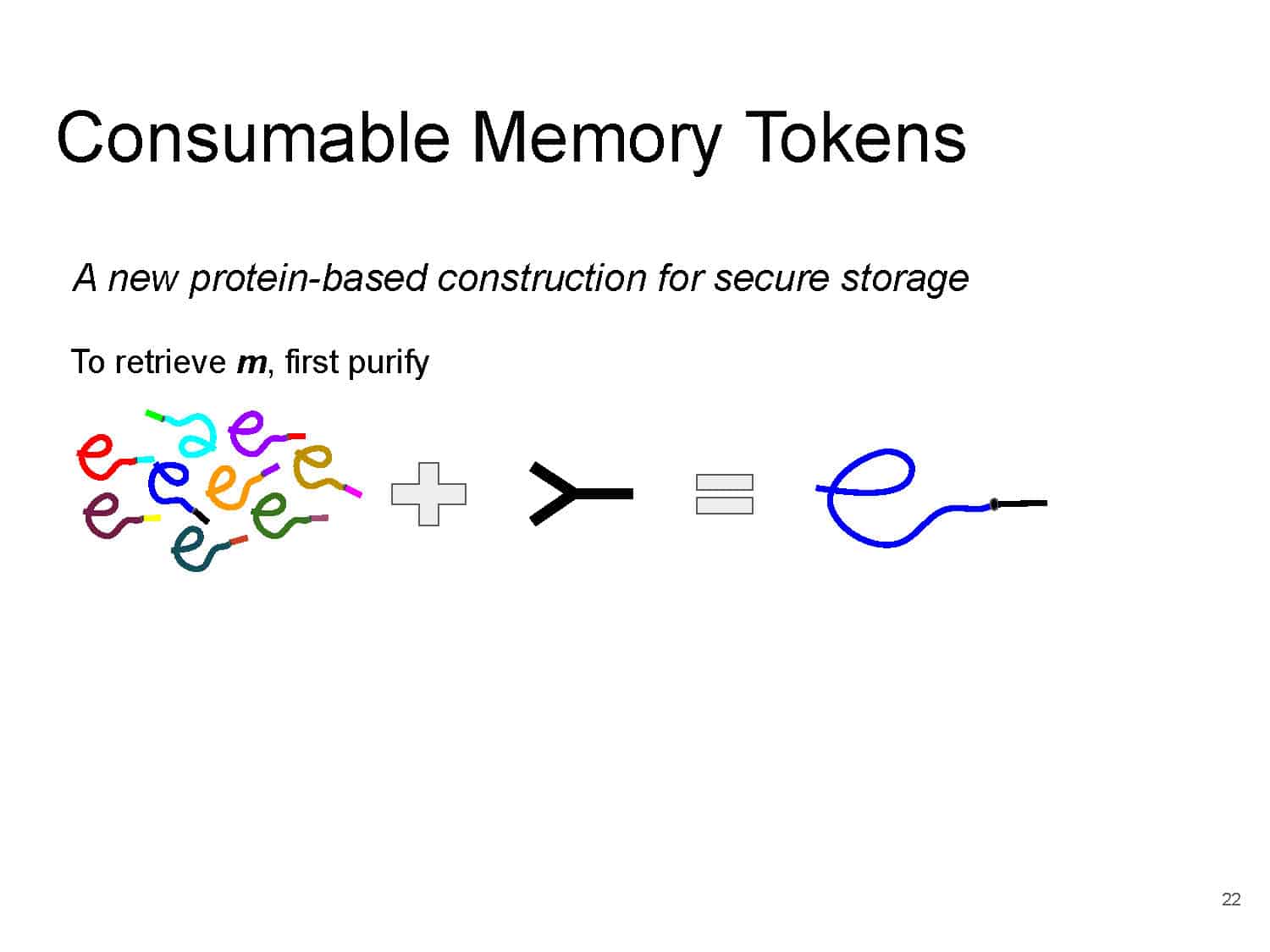
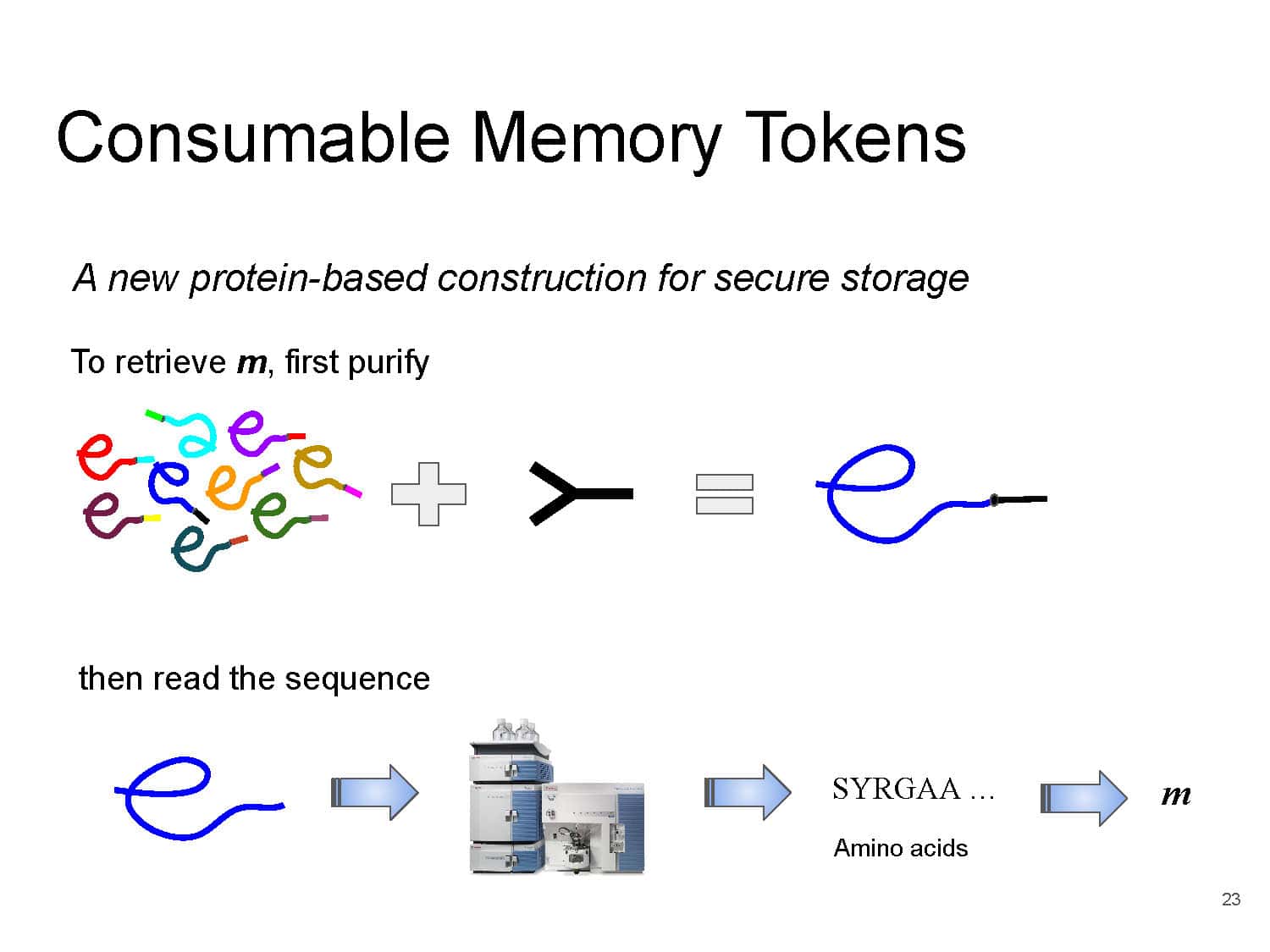
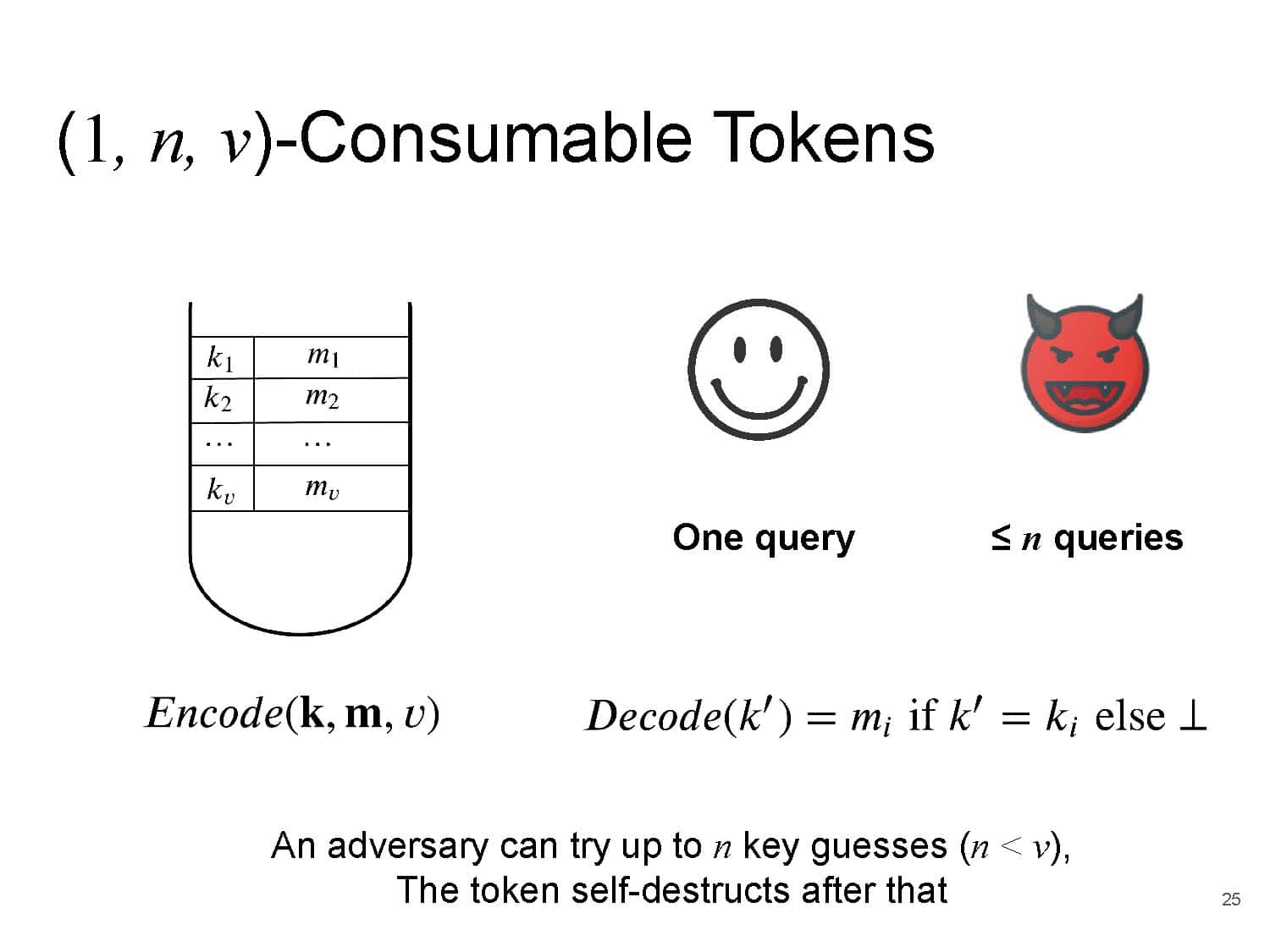
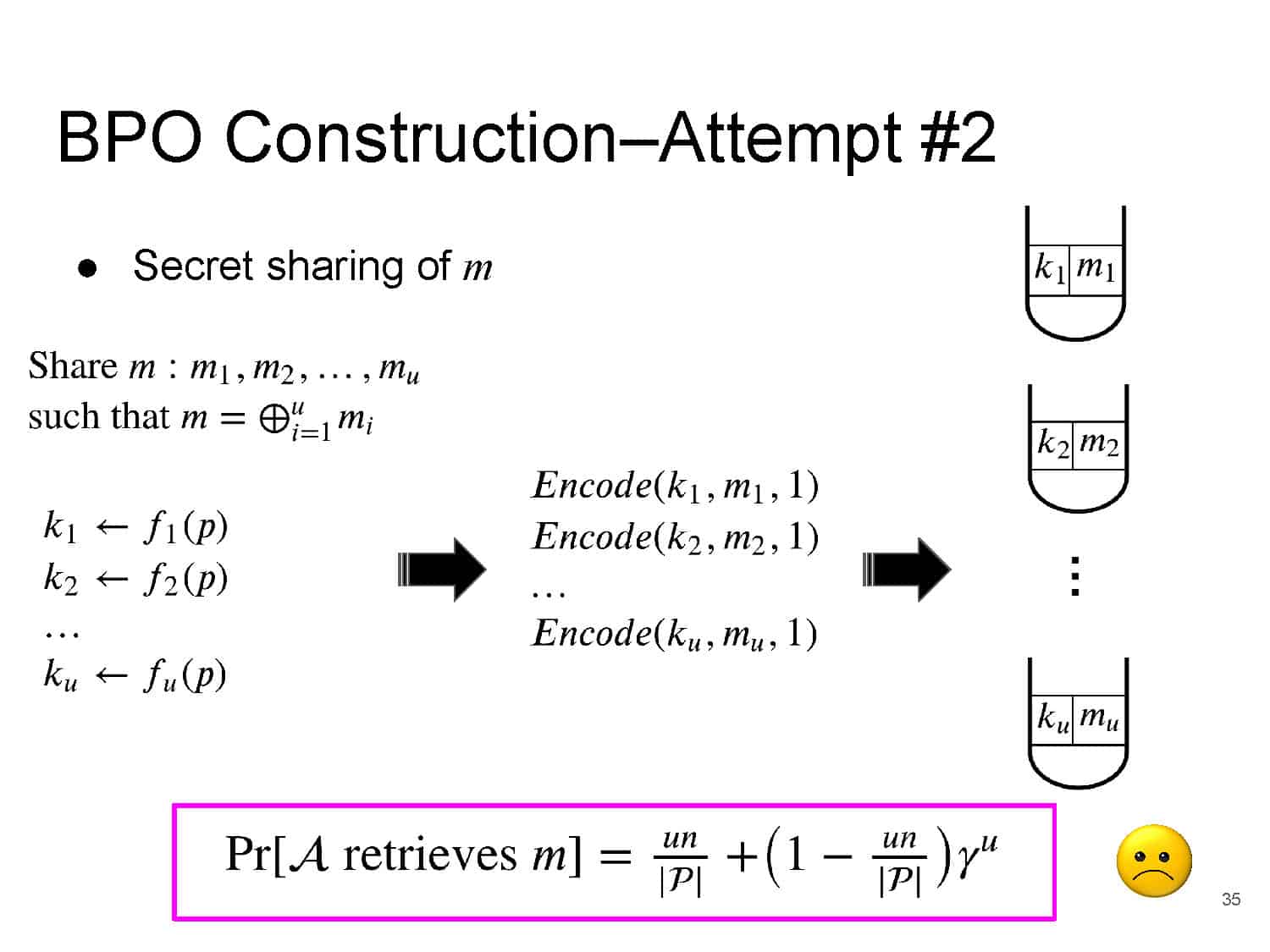
We propose a mechanism for generating and manipulating protein polymers to obtain a new type of consumable storage that exhibits intriguing cryptographic “self-destruct” properties, assuming the hardness of certain polymer-sequencing problems.
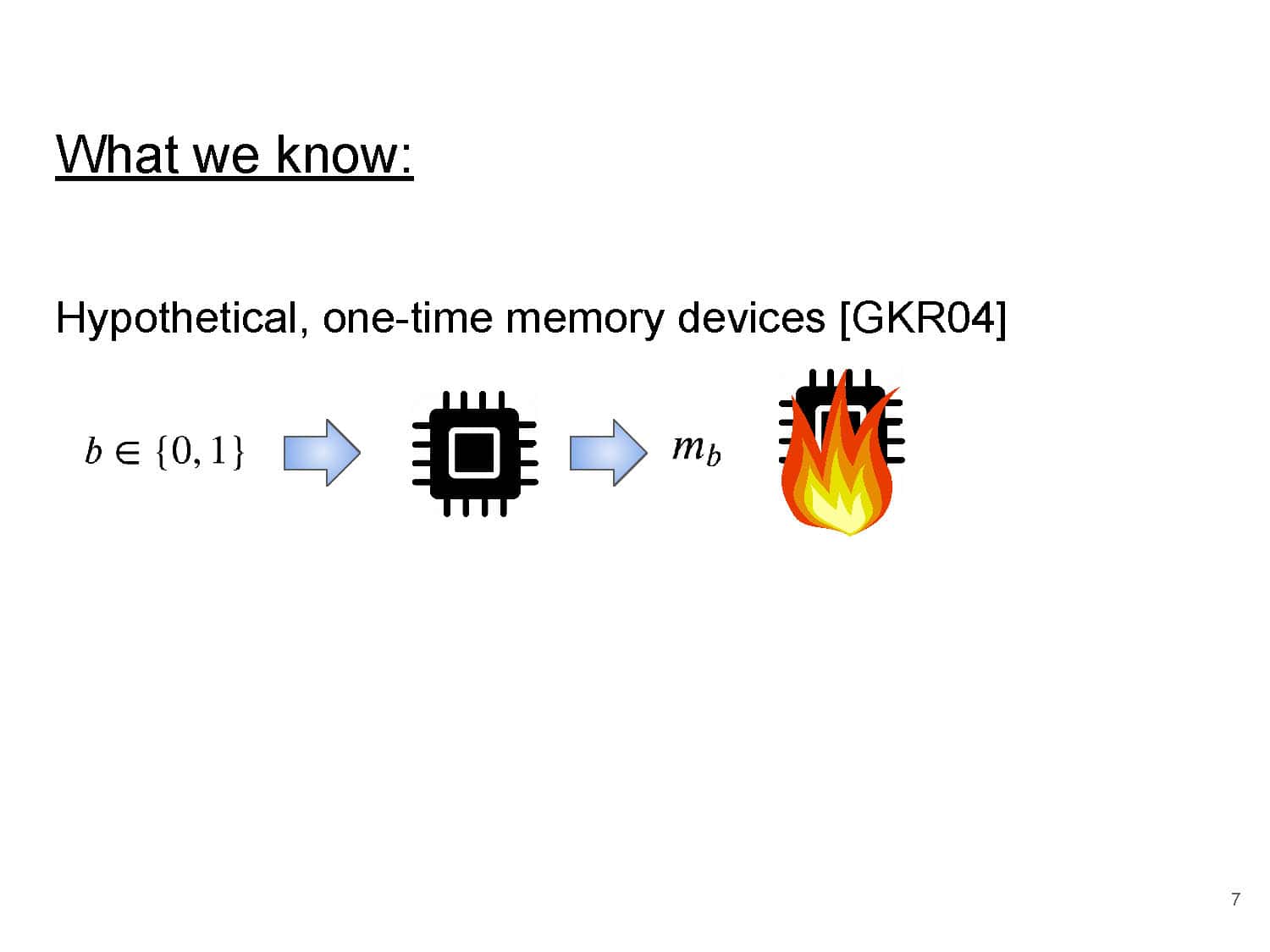
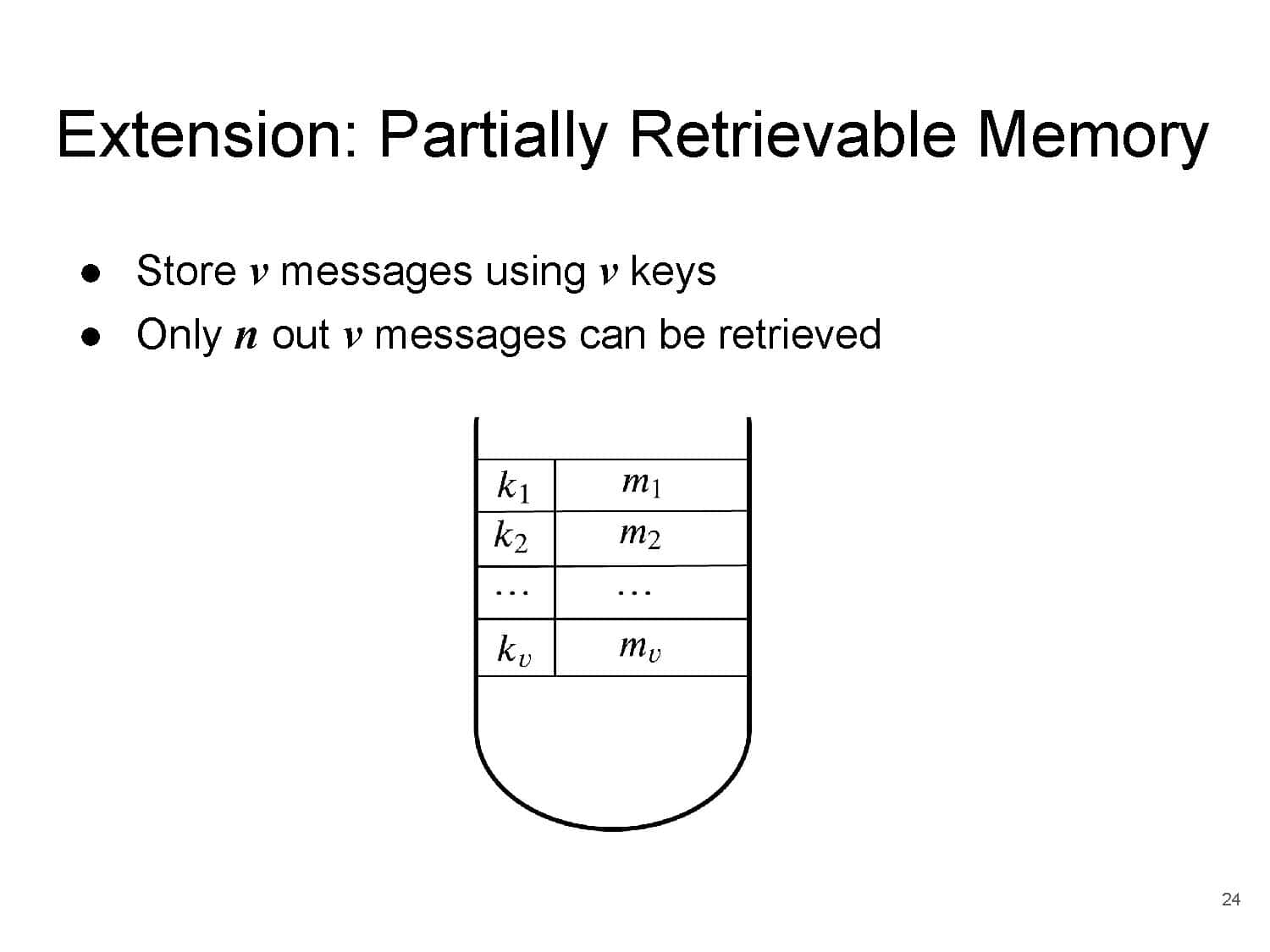
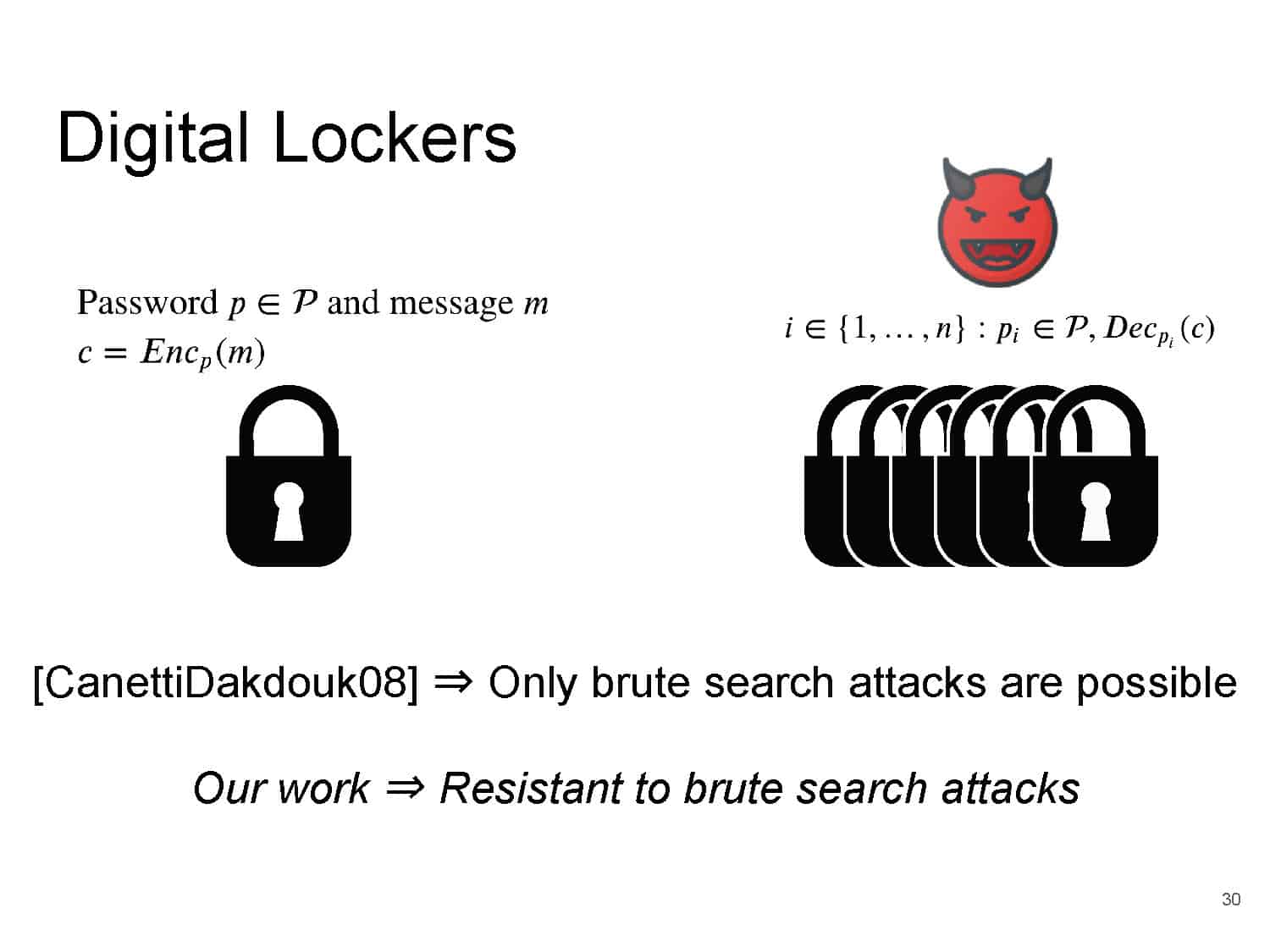
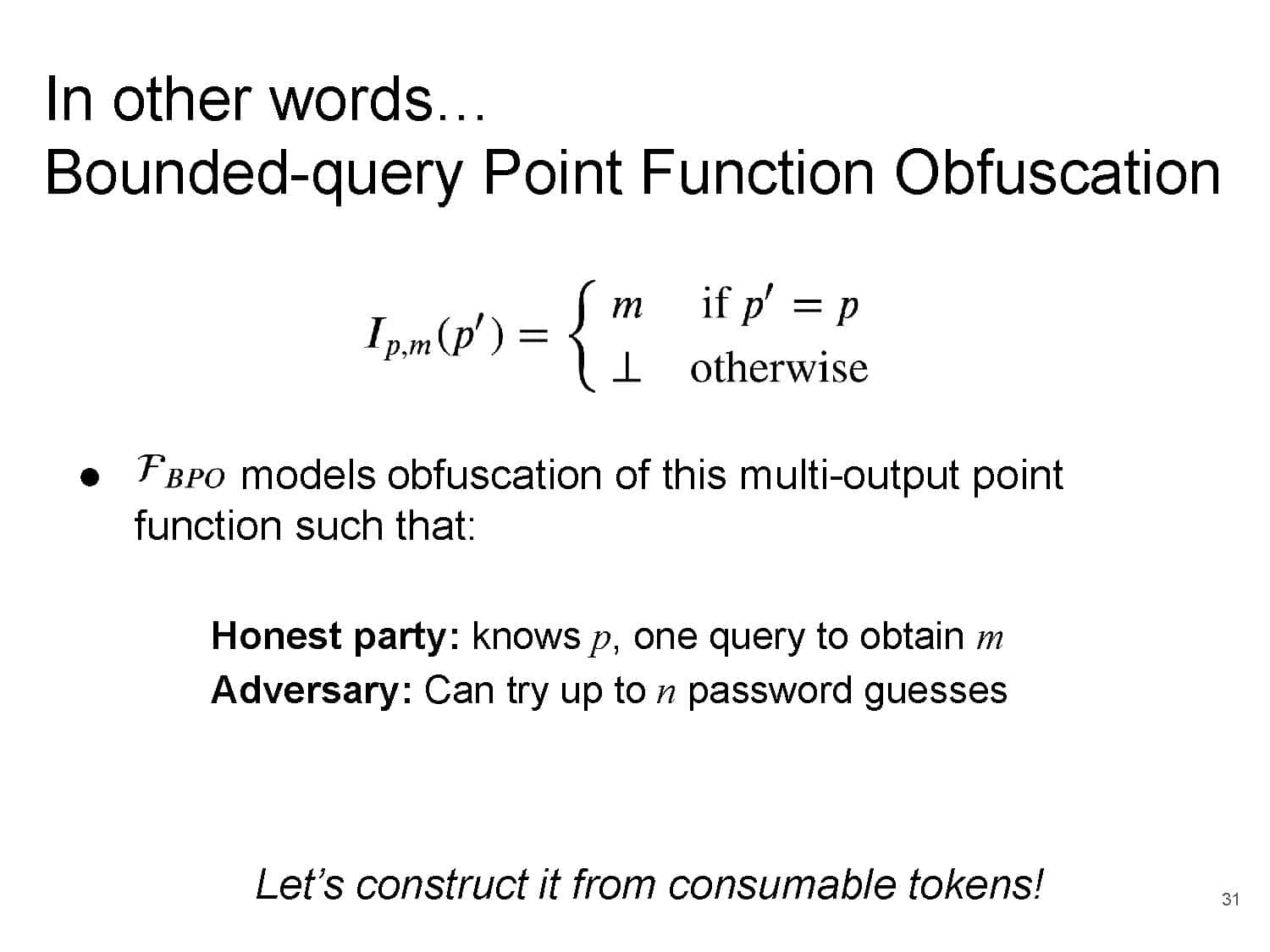
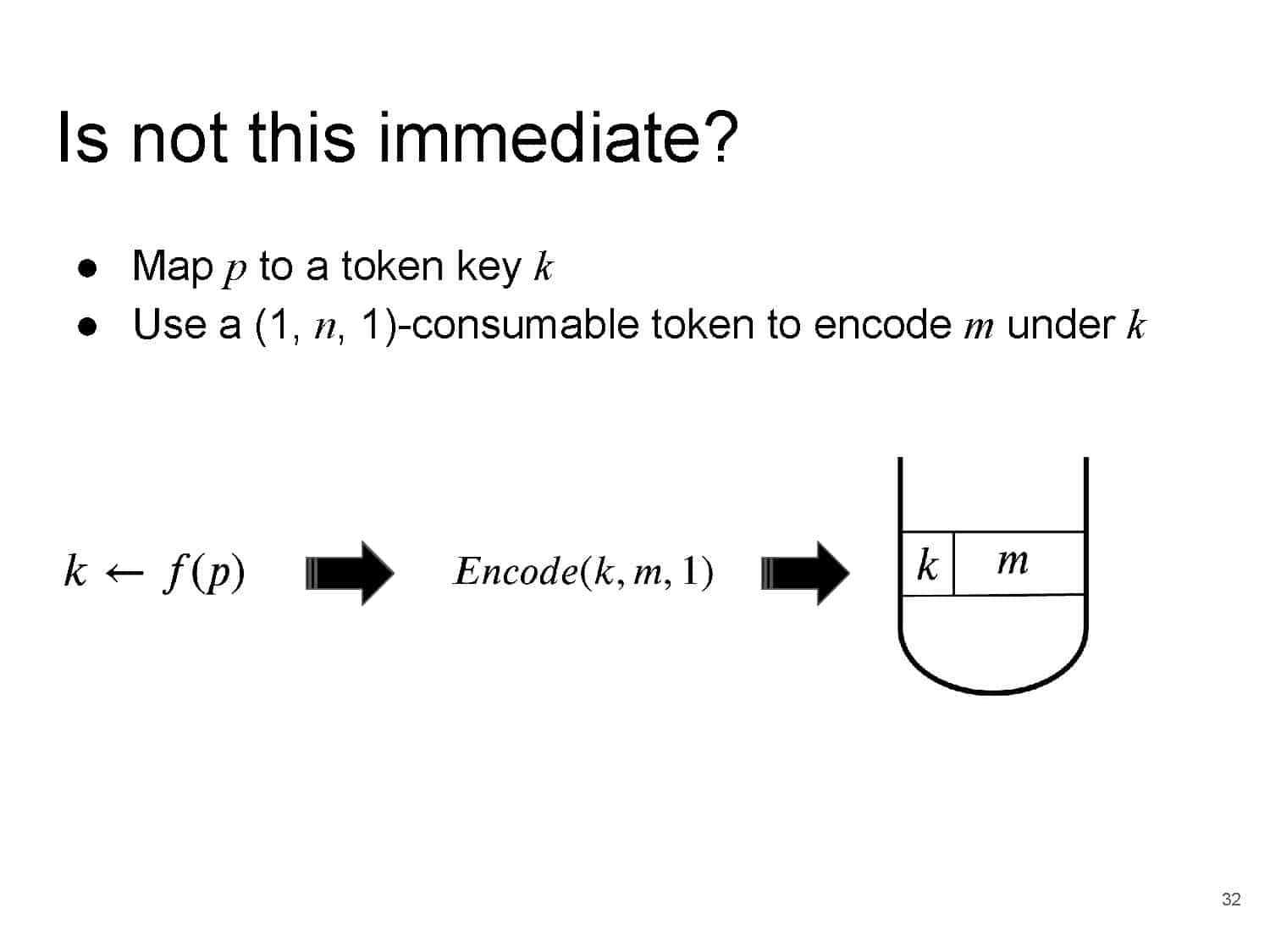
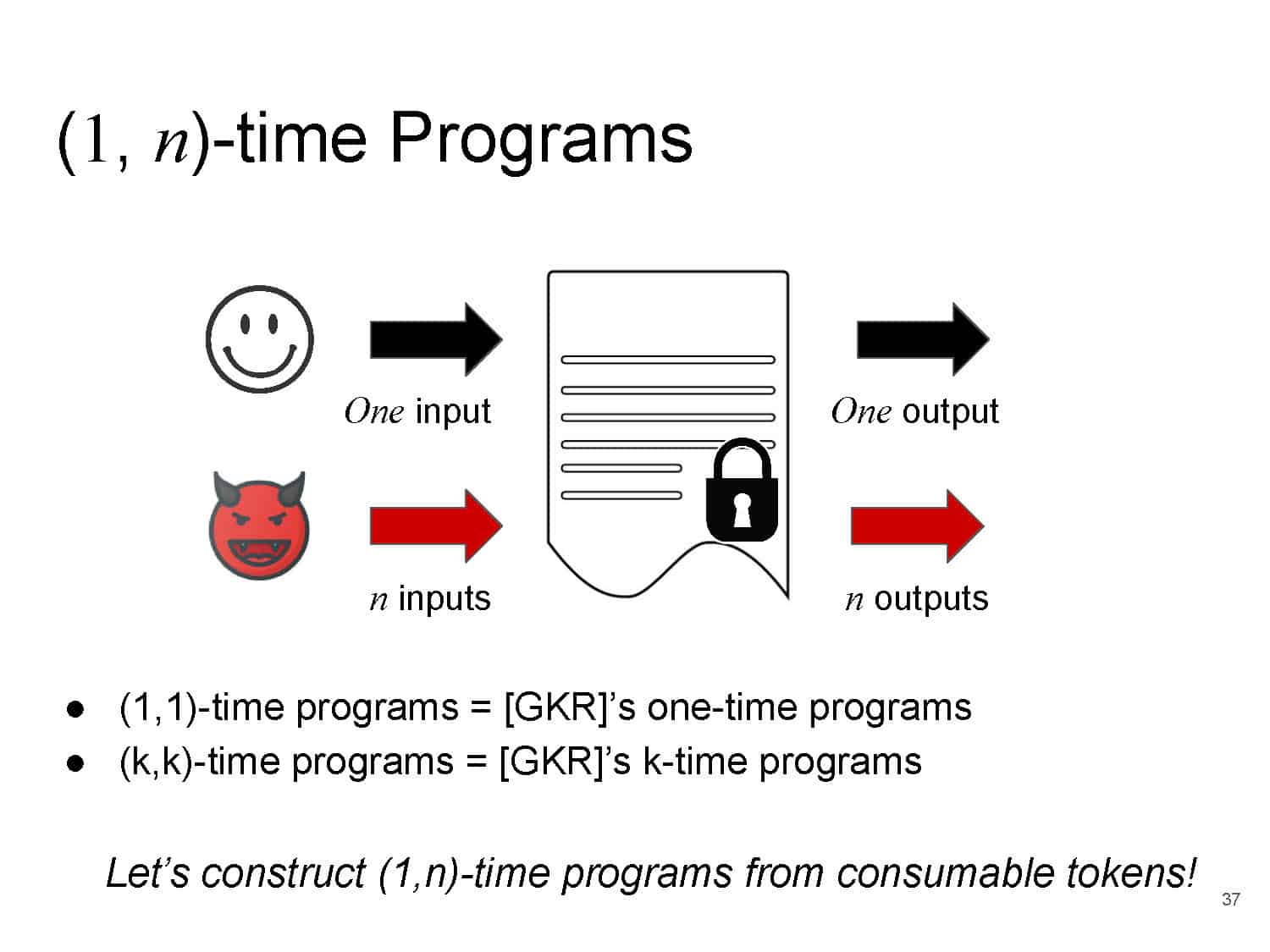
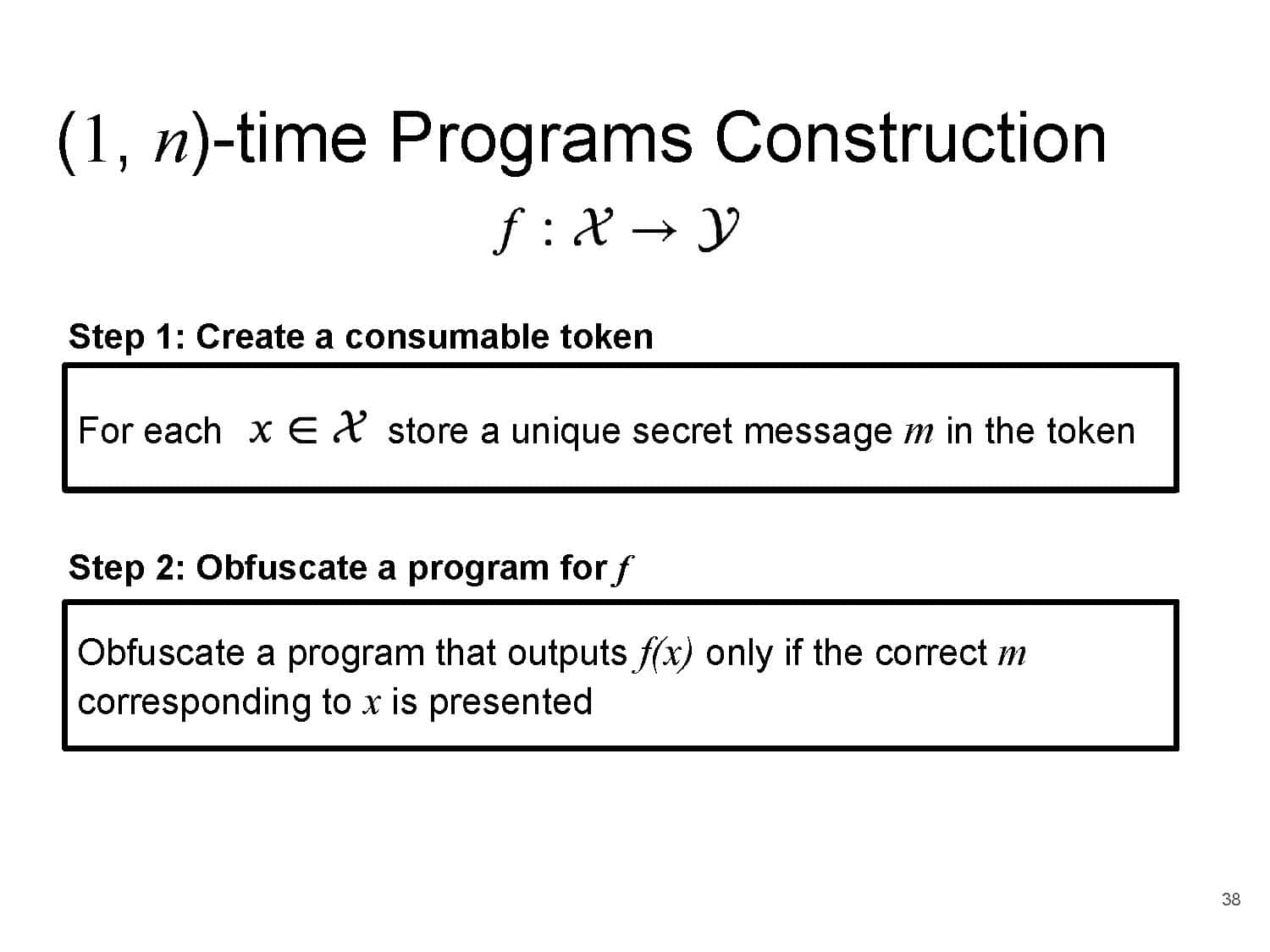
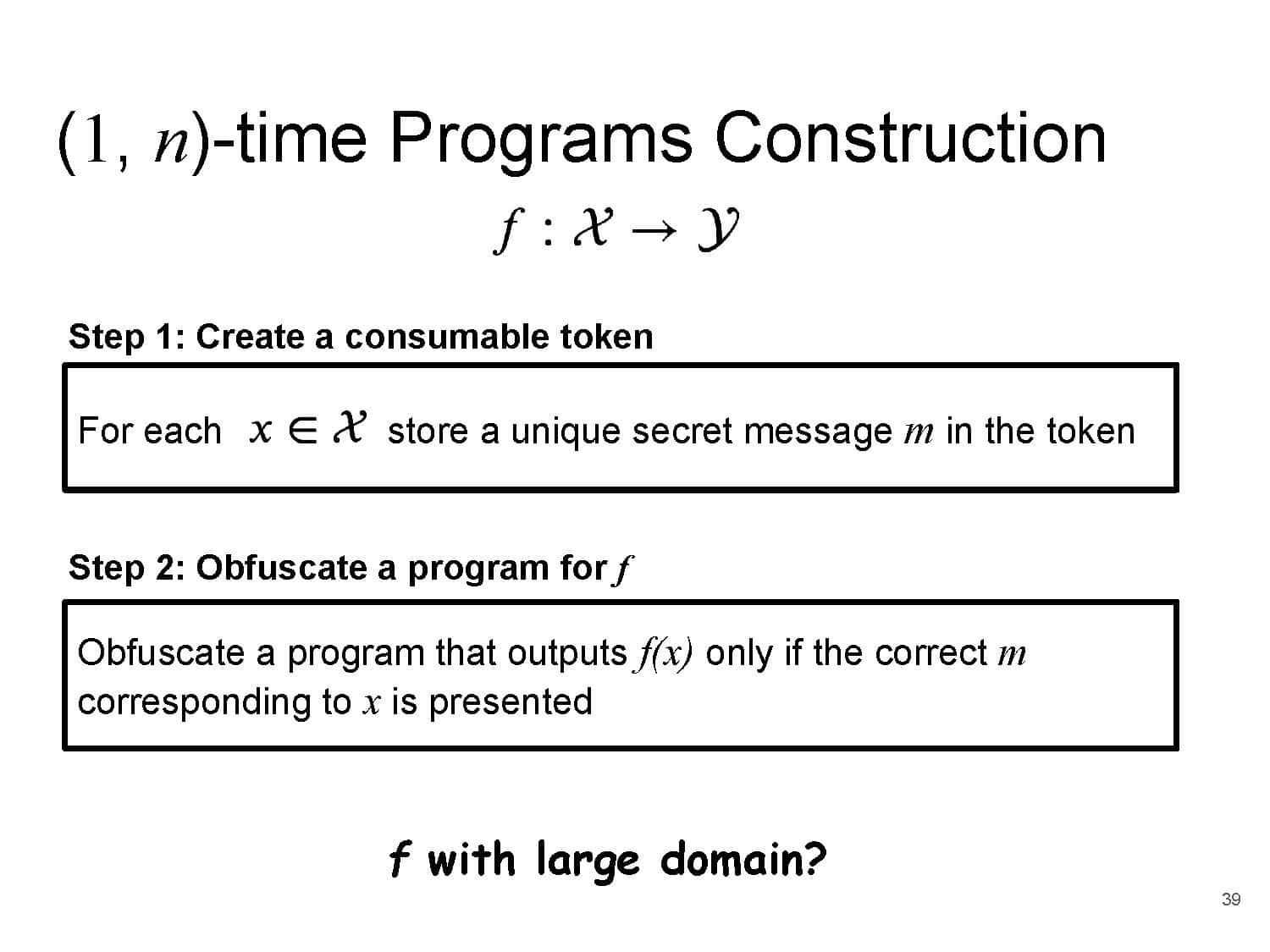
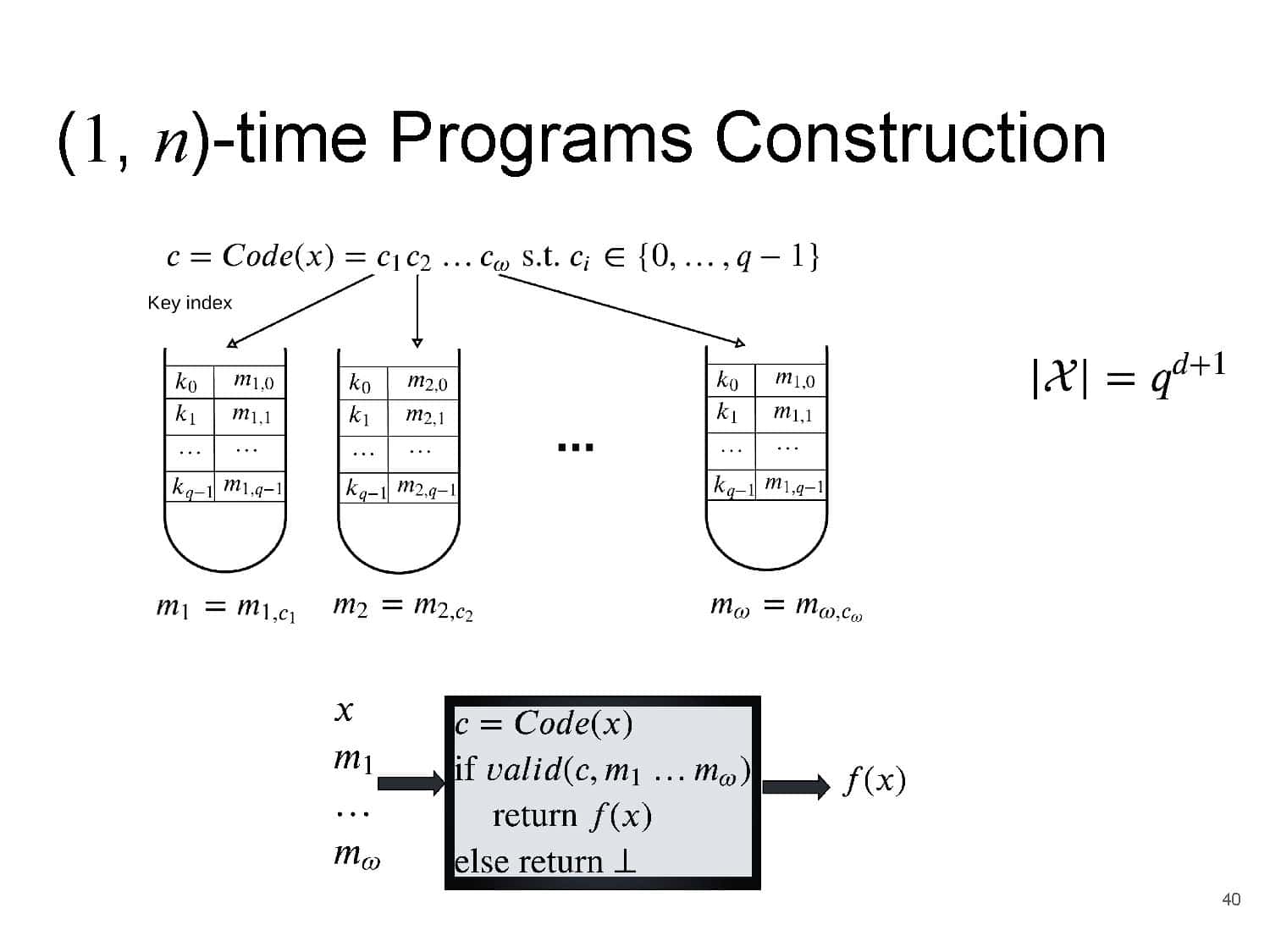
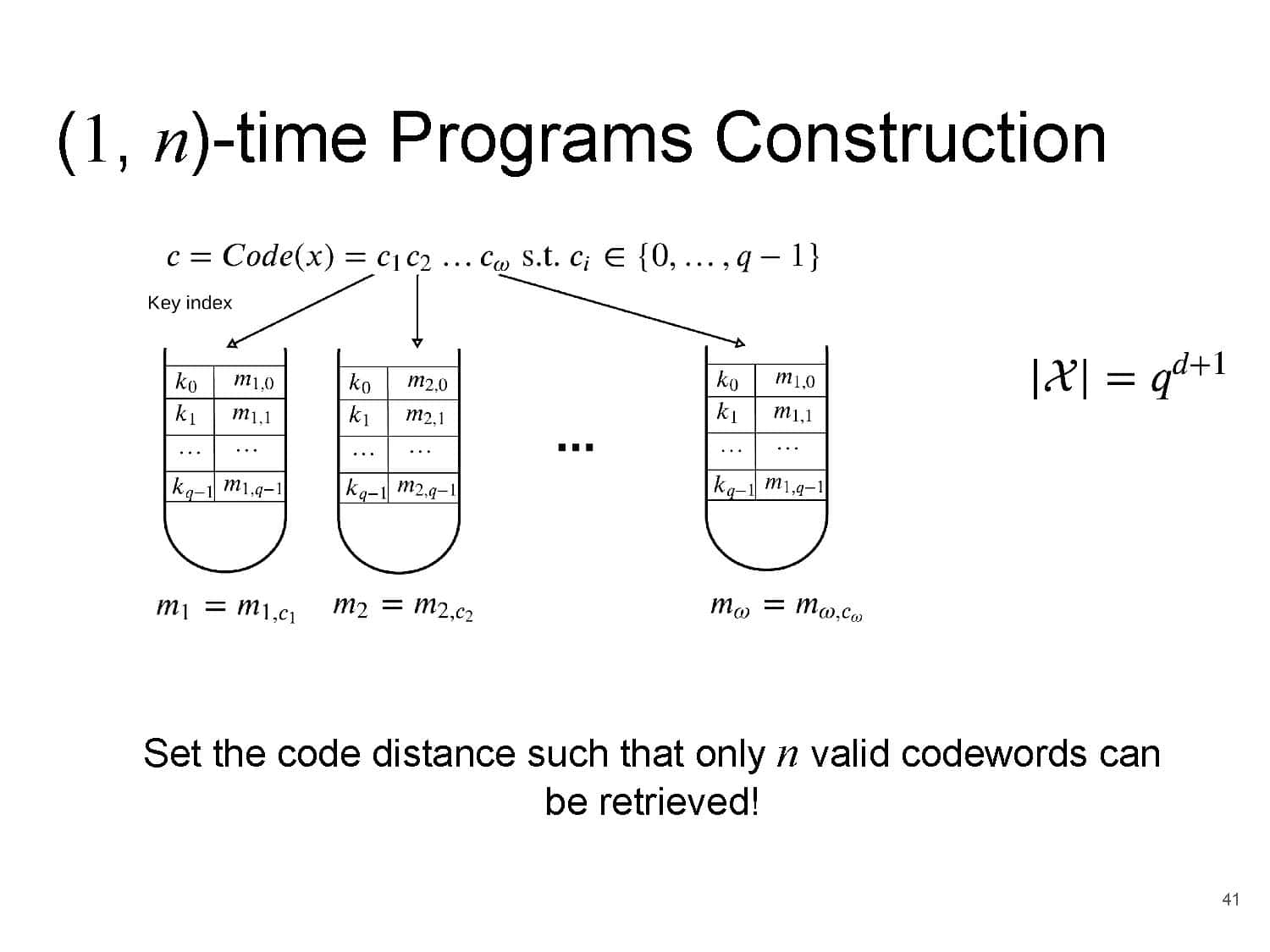
To demonstrate the cryptographic potential of this technology, we first develop a formalism that captures (in a minimalistic way) the functionality and security properties provided by the technology. Next, using this technology, we construct and prove security of two cryptographic applications that are currently obtainable only via trusted hardware that implements logical circuitry (either classical or quantum). The first application is a password-controlled secure vault where the stored data is irrecoverably erased once a threshold of unsuccessful access attempts is reached. The second is (a somewhat relaxed version of) one-time programs, namely a device that allows evaluating a secret function only a limited number of times before self-destructing, where each evaluation is made on a fresh user-chosen input.
Finally, while our constructions, modeling, and analysis are designed to capture the proposed polymer-based technology, they are sufficiently general to be of potential independent interest.
Challenges:
Cryptography: can we avoid the strong assumption of indistinguishability obfuscation when building bounded execution programs?
Biology: can we develop more sophisticated and accurate protein sequencing procedures/machinery to overcome the limitations we have now on protein-based data storage/retrieval?